What is Suhosin?
Suhosin (pronounced ‘su-ho-shin’) is an advanced protection system for PHP installations. It was designed to protect servers and users from known and unknown flaws in PHP applications and the PHP core. Suhosin comes in two independent parts, that can be used separately or in combination. The first part is a small patch against the PHP core, that implements a few low-level protections against buffer overflows or format string vulnerabilities and the second part is a powerful PHP extension that implements numerous other protections.
Why Suhosin?
The most important question for new users of Suhosin is, why they should use Suhosin at all, if it is really necessary and what they gain by using the patch, the extension or a combination of both.
The answer to this question depends on what your usage of PHP is. If you are using PHP only for your own server and only for your own scripts and applications, then you can judge for yourself, if you trust your code enough. In that case you most probably don’t need the Suhosin extension. Because most of it’s features are meant to protect servers against vulnerable programming techniques. However PHP is a very complex programming language with a lot of pitfalls that are often overseen during the development of applications. Even PHP core programmers are writing insecure code from time to time, because they did not know about a PHP pitfall. Therefore it is always a good idea to have Suhosin as your safety net. The Suhosin-Patch on the other hand comes with Zend Engine Protection features that protect your server from possible buffer overflows and related vulnerabilities in the Zend Engine. History has shown that several of these bugs have always existed in previous PHP versions.
If you are not only running your own PHP scripts but are also hosting 3rd party PHP applications for yourself or even for possible customers, then you cannot trust the code quality of the PHP applications you use. Unfortunately it is a fact that the pitfalls of the PHP language are not widely known among programmers. Many of these pitfalls are also not documented in the PHP-Security books that have been released during the last year. This is mainly caused by the fact, that the books were written in a hurry to be the first in market and because most of these books were not written by security professionals but by PHP programmers. The worst of these books is the one by Oreilly which contains examples that might fix the problem described but introduces more dangerous vulnerabilities into your application.
Another common error in these books is that they spread the urban legend that the most dangerous problem within PHP “remote code inclusion vulnerabilities” can be fixed by disabling allow_url_fopen in the configuration (or allow_url_include in PHP 5.2.x). This information is simply wrong, because these configuration directives do NOT protect against attacks through php://input or data:// URLs. Our Suhosin and the former Hardening-Patch are the only available protections that close all URL include attacks.
Summed up, it is your free choice to use Suhosin. If you want additional protection for your servers and your business, we can only recommend strongly that you use the extension and the patch. Always keep in mind that you are not only protecting yourself and your users, but also other people on the internet, that might get attacked by your server after it has been turned into a (Spam-/DDOS-)attack drone.
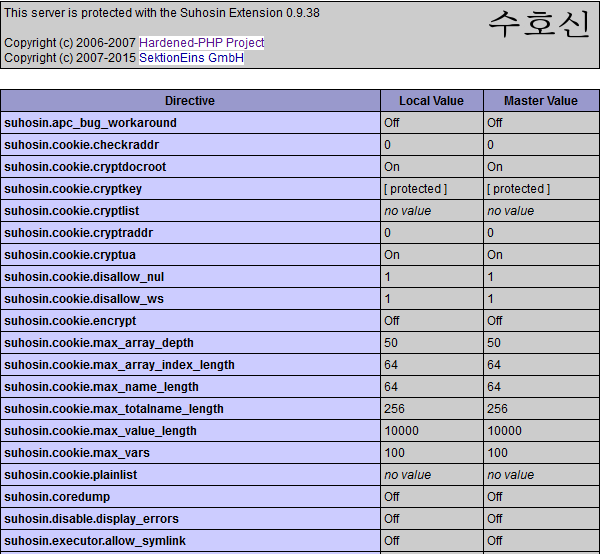
Feature List
Engine Protection
Protects the internal memory manager against bufferoverflows with Canary and SafeUnlink Protection Protects Destructors of Zend Hashtables Protects Destructors of Zend Linked-Lists Protects the PHP core and extensions against format string vulnerabilities Protects against errors in certain libc realpath() implementations
Misc Features
Protection Simulation mode :!: Adds the functions sha256() and sha256_file() to the PHP core Adds support for CRYPT_BLOWFISH to crypt() on all platforms Transparent protection of open phpinfo() pages EXPERIMENTAL SQL database user protection
Runtime Protection
Transparent Cookie Encryption :!: Protects against different kinds of (Remote-)Include Vulnerabilities disallows Remote URL inclusion (optional: black-/whitelisting) disallows inclusion of uploaded files optionally stops directory traversal attacks Allows disabling the preg_replace() /e modifier Allows disabling eval() Protects against infinite recursion through a configureabel maximum execution depth Supports per Virtual Host / Directory configureable function black- and whitelists Supports a separated function black- and whitelist for evaluated code Protects against HTTP Response Splitting Vulnerabilities Protects against scripts manipulating the memory_limit Protects PHP‘s superglobals against extract() and import_request_vars() Adds protection against newline attacks to mail() Adds protection against 0 attack on preg_replace()
Session Protection
Transparent encryption of session data :!: Transparent session hijacking protection :!: Protection against overlong session identifiers Protection against malicious chars in session identifiers
Filtering
Filters ASCIIZ characters from user input Ignores GET, POST, COOKIE variables with the following names: GLOBALS, _COOKIE, _ENV, _FILES, _GET, _POST, _REQUEST _SERVER, _SESSION, HTTP_COOKIE_VARS, HTTP_ENV_VARS HTTP_GET_VARS, HTTP_POST_VARS, HTTP_POST_FILES HTTP_RAW_POST_DATA, HTTP_SERVER_VARS, HTTP_SESSION_VARS Allows enforcing limits on REQUEST variables or separated by type (GET, POST, COOKIE) Supports a number of variables per request limit Supports a maximum length of variable names [with and without indicies] Supports a maximum length of array indicies Supports a maximum length of variable values Supports a maximum depth of arrays Allows only a configureable number of uploaded files Supports verification of uploaded files through an external script Supports automatic banning of uploaded ELF executables Supports automatic banning of uploaded binary files Supports automatic stripping of binary content in uploaded files Configureable action on violation just block violating variables send HTTP response code redirect the browser execute another PHP script
Logging
Supports multiple log devices (syslog, SAPI module error log, external logging script) Supports freely configureable syslog facility and priority Supports log device separated selection of alert types to log Alerts contain filename and linenumber that triggered it Alerts contain the IP address of the user triggering it The IP Address can also be extracted from X-Forwarded-For HTTP headers (f.e. for reverse proxy setups)
How To Install Suhosin
https://panel.bullten.net/knowledgebase/60/Installing-Suhosin-in-CWP.html